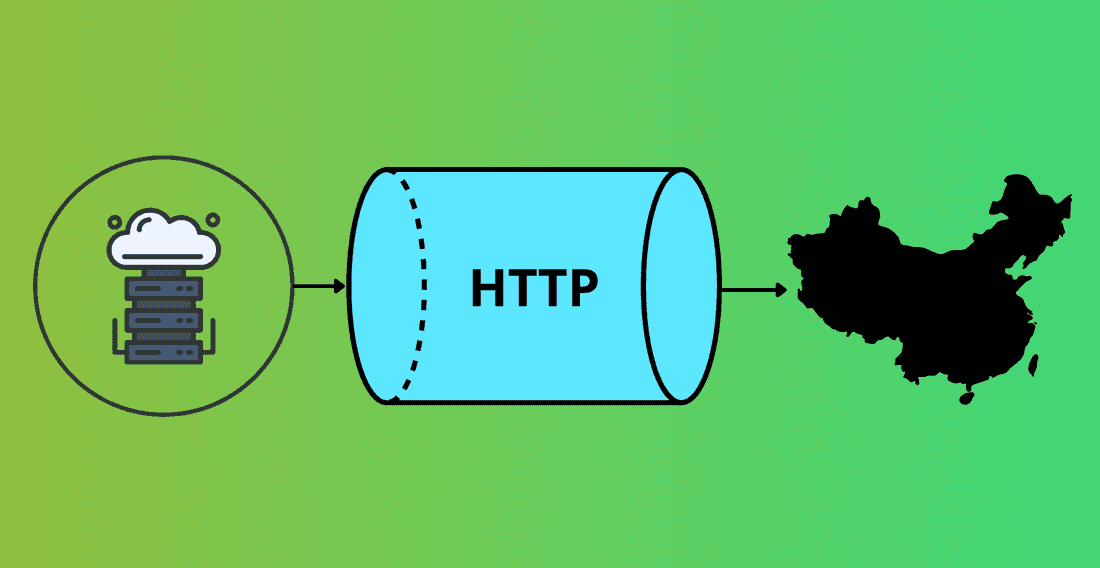
HTTP Tunnel Solution for China: Connect Back to Your Backend Services Outside China
If you want to launch an app in China without rebuilding your entire backend stack locally, one of the biggest technical challenges is usually: how do you let your China deployment securely access backend services that still run outside Mainland China?
For many international companies, the preferred architecture is straightforward: keep the core backend in the US, Europe, or Singapore; deploy only the minimum required frontend and integration components inside China; and maintain a private, reliable path between China and the overseas backend. The problem is that this is much harder in practice than it sounds.
Traditional VPN solutions such as OpenVPN, IPSec, and WireGuard may be inexpensive and easy to set up, but in real cross-border scenarios involving China, they are often unstable over the public internet. Dedicated connectivity products such as AWS Direct Connect can improve reliability, but they introduce significantly higher setup, rental, and traffic costs.
For many overseas app publishers, an HTTP tunnel approach is one of the most cost-effective ways to solve this problem. This guide explains why this architecture works well for China deployment scenarios, and why ZTM (Zero Trust Mesh) is a strong option for connecting lightweight China-side services back to existing backend systems outside China.
What Is the Real Problem?
A very common China deployment pattern looks like this: a lightweight frontend, gateway, or service node deployed in Mainland China; the main backend platform still hosted overseas; and selected local services, such as SMS, payment, or compliance-sensitive integrations, running in China.
This model is attractive because it allows you to enter the China market without migrating your full application stack into China from day one. However, it creates a critical networking requirement. Your China-side systems need to access overseas backend services in a way that is private, stable, secure, affordable, and operationally simple.
In some cases, the requirement is stricter still. Certain functions involving personal data, telecom resources, or local platform integrations may need to originate from a China IP address. For example, if your app uses a China-based SMS provider such as Alibaba Cloud SMS, calling the API directly from an overseas cloud region may not be operationally suitable or compliant for some projects. That means your architecture may need to support both of the following flows: China-side services connecting back to overseas backend systems, and overseas backend systems sending requests out through a China-based node. This is why a simple “public API over HTTPS” approach is often not enough.
Why Traditional VPNs Usually Fail for This Use Case
For most engineering teams, the first idea is to build a site-to-site VPN. That is reasonable in a normal international deployment, but China introduces additional constraints.
The key issue is not your IPSec or strongSwan configuration. The larger problem is that common VPN protocols are easy to identify as VPN traffic and will be blocked by the Great Firewall. In real-world cross-border scenarios, this creates a significant stability risk: OpenVPN traffic can be identified and interrupted, IPSec site-to-site tunnels can be throttled or blocked, and WireGuard may also be detected as a VPN protocol. Changing configuration details often does not solve the root problem because the challenge is not “how do I tune the VPN better?” it is that the protocol itself looks like a VPN on the wire.
If you plan to connect something like GCP Europe to AWS China over the public internet with a conventional site-to-site VPN, it may work temporarily, but it is not a reliable long-term production choice. From a business perspective, this instability creates real product risk: slower rollout in China, unpredictable downtime, a heavier support burden for your engineering team, difficult incident debugging, and a poor user experience.
That is why many teams eventually stop looking for a better VPN configuration and start looking for a different transport model entirely.
Why Dedicated Private Lines Are Not Always the Right First Step
At the other end of the spectrum, you have dedicated connectivity options such as AWS Direct Connect, Azure ExpressRoute, Alibaba Cloud Express Connect, and Tencent Cloud Direct Connect. These solutions are often more stable and more enterprise-friendly than public internet VPNs, but they come with clear trade-offs: higher fixed monthly costs, additional setup complexity, carrier coordination, longer provisioning times, and less flexibility for early-stage projects.
If you are already operating a large China business, this may be justified. But if you are still testing market fit, building an MVP, or trying to keep initial China infrastructure lean, this can be too expensive and too heavy. For many companies, the question is not “what is the most enterprise-grade option possible?” — it is: what is the lowest-cost architecture that is still reliable enough to support a real China deployment? That is where an HTTP tunnel solution becomes attractive.
What is an HTTP Tunnel Solution?
An HTTP tunnel solution creates a private communication channel over HTTPS or HTTP/2 instead of using a classic VPN protocol. Rather than exposing a recognisable VPN handshake, the traffic looks much closer to ordinary encrypted web traffic. This gives you a more discreet transport path for cross-border communication.
That does not mean any HTTP tunnel is guaranteed to work in every scenario. No public internet method should be described that way. But in practice, this architecture can be significantly more robust than a traditional software VPN for connecting a China-side node to backend services outside China. From an implementation perspective, it offers a useful middle path: lower cost than a dedicated private line, more practical than OpenVPN or IPSec over the public internet, and easier to roll out than re-architecting your full backend into China.
Why ZTM Is a Strong Choice
ZTM (Zero Trust Mesh) is an open-source networking platform built around HTTP/2 tunnels, TLS encryption, and certificate-based authentication. It is designed to support private connectivity across internet gateways and firewalls, and it can scale from a small deployment to a multi-node mesh architecture. For overseas app publishers targeting China, that makes it especially useful.

1. It uses HTTP/2 instead of a classic VPN protocol. ZTM uses HTTP/2 on the wire, which makes the traffic pattern much closer to standard HTTPS than to a traditional VPN. In practical China cross-border scenarios, this is often far more workable than exposing OpenVPN, IPSec, or WireGuard directly.
2. It supports mutual TLS, not just normal HTTPS. A normal public web application typically uses one-way TLS: the client verifies the server, and application-layer identity comes later through login, token, OAuth, JWT, or cookies. ZTM uses mutual TLS between nodes, so the transport layer itself enforces trust before any communication begins. This gives you a more controlled, zero-trust-style architecture for private service access.
3. It supports more than just web requests. You are not limited to exposing a single public app endpoint. The tunnel can serve as a controlled transport path for REST or HTTPS APIs, WebSocket traffic, SSH, internal admin tools, service-to-service communication, and other application-layer protocols. This means your China node does not need to expose every internal backend service individually.
4. It supports bidirectional traffic. Many companies initially think only about one direction: the China frontend calling the overseas backend. But in production, the reverse direction often matters too. The overseas backend may need to trigger a local SMS provider, access a service that should originate from a China IP, or route specific outbound operations through a China-side node. A bidirectional tunnel is therefore much more useful than a simple “public frontend calls a public API” model.
5. It supports multi-node mesh deployment. ZTM is not limited to a single point-to-point tunnel. It can support a multi-node mesh topology, which is valuable for improving resilience over time through more than one China node, more than one overseas node, high-availability paths, regional traffic separation, and controlled failover design. This gives you a production-ready upgrade path without committing to expensive leased-line infrastructure upfront.
What Makes This Better Than Just Using HTTPS Directly?
A common question is: if ZTM uses HTTP/2 and HTTPS-like traffic anyway, why not simply expose your backend and call it directly over HTTPS?
The two approaches solve different problems. With direct HTTPS, the client connects straight to a public service endpoint, security relies on server-side TLS plus application-layer auth, and each backend service may need its own exposure model. This works well for normal internet-facing applications, but it is not ideal when you want a private bridge between your China deployment and your overseas internal services.
With ZTM, a trusted agent connects to a hub or peer using mutual TLS, the transport channel itself is authenticated, multiple internal services can run through one authorised path, and traffic can flow in both directions between China and overseas systems without exposing every backend service publicly. That makes it much closer to a private application network than a standard public HTTPS setup.
Why This Matters Commercially
From a business perspective, this architecture helps international app publishers solve four major problems at the same time.
Lower China launch cost. You do not need to duplicate your entire backend stack inside China. You can keep the expensive and complex parts of your platform where they already are.
Faster time to market. You can deploy a lightweight China entry architecture much faster than building a full local infrastructure or waiting for dedicated cross-border private networking.
Better control over compliance-related flows. When selected API requests need to originate from China, you can route them through a controlled China-side node instead of redesigning your whole backend.
More predictable operations than a standard VPN. This reduces the risk of unstable cross-border connectivity becoming the bottleneck in your China rollout.
Typical Architecture
China side. Deploy a lightweight node in Mainland China that handles app-facing frontend or gateway functions, local integrations such as China SMS or local APIs, and controlled entry or exit into the tunnel.
Overseas side. Keep your core backend systems where they already run: application APIs, user services, business logic, operational dashboards, internal admin tools, and selected databases and support services where legally appropriate.
Tunnel layer. Use ZTM to create a private HTTP/2-based tunnel between the China node and the overseas environment. This creates a controlled path for China-to-overseas backend access, overseas-to-China API egress, internal service communication, and private protocol transport without exposing multiple public-facing services.
Performance Expectations
Actual performance depends on cloud region selection, ISP routing quality, carrier path conditions, protocol behaviour, and application traffic pattern. In project testing, this architecture has delivered HTTP/2 tunnel latency of around 100ms in suitable scenarios. For many backend access patterns, that is sufficient to support production workloads such as API calls, internal service communication, control-plane traffic, administrative access, and selected business workflows.
This approach is not designed to replace every high-throughput enterprise networking scenario. But for many app publishers, it is exactly the right balance of cost, simplicity, and practical reliability.
Frequently Asked Questions
Is a traditional VPN enough for connecting China to an overseas backend? Usually not as a long-term production solution. Traditional VPN protocols such as OpenVPN, IPSec, and WireGuard may work temporarily, but they are often too fragile over the public internet in real China cross-border scenarios. The issue is often not the specific VPN software, but the fact that the traffic is recognisable as VPN traffic and will be blocked by the Great Firewall.
Is there a better IPSec or strongSwan configuration for this? Usually no. In this kind of use case, the main problem is not a missing configuration trick. If the traffic is being classified as a VPN tunnel, changing your strongSwan parameters is unlikely to make the connection reliably production-grade.
Why not just use AWS Direct Connect or another dedicated line? Because it is often too expensive and operationally heavy for an early-stage deployment. Dedicated private networking can be the right choice for larger businesses, but for many companies entering China, the cost and setup complexity are difficult to justify at the beginning.
What is the advantage of a HTTP tunnel? A HTTP tunnel gives you a private communication path over HTTP/2 or HTTPS-like transport instead of a classic VPN protocol. In practice, this can be a much more workable option for China-facing deployments that need private access to overseas backend systems.
Why is ZTM better than directly exposing my backend over HTTPS? Because ZTM is not just public HTTPS. It creates an authenticated transport layer between trusted nodes, supports multiple internal services over a single tunnel, and allows bidirectional connectivity without exposing every backend component directly to the internet.
Can this architecture support calls that must originate from a China IP? Yes. That is one of its biggest practical advantages. A China-side node can be used as the controlled origin point for selected outbound requests, such as local SMS or other China-only integrations.
Is this suitable for high availability? Yes, potentially. Because ZTM supports multi-node mesh topologies, it can be deployed in a more resilient way than a simple single-tunnel setup. That makes it a strong candidate for high-availability designs as the project grows.
Is it suitable for every company? No. If you need guaranteed carrier-grade SLAs, very high constant throughput, or a formally managed enterprise private network from day one, dedicated private connectivity may still be the better choice. But for many app publishers — especially those trying to minimise launch cost — this is one of the best practical solutions available.
When This Approach Makes the Most Sense
This model is a good fit if you want to promote an app in China without rebuilding the full backend locally, your core systems already run outside China, you only need a lightweight deployment inside China, you need a private channel between China and overseas systems, some requests need to originate from a China IP, traditional VPNs are too unstable, or dedicated private networking is too expensive at the current stage.
How Can AppInChina Help?
For overseas app publishers, cross-border backend connectivity is often one of the most important and least obvious parts of a China deployment strategy. Traditional VPNs are low-cost but frequently too fragile for real production use. Dedicated private lines are more robust but often too expensive for a lean market-entry phase.
That is why a HTTP tunnel architecture deserves serious attention. A solution such as ZTM gives you a practical middle path: lower cost than leased lines, more discreet than classic VPNs, private connectivity back to overseas backend systems, support for China-originated outbound integrations, and flexibility for multi-node and high-availability deployment.
At AppInChina, we can help with:
- Architecture design, advising on the right cross-border connectivity model for your deployment stage and infrastructure requirements
- China-side infrastructure setup, deploying and configuring lightweight nodes in Mainland China to minimise your local footprint
- ZTM configuration and integration, connecting your China-side deployment back to your existing overseas backend systems
- Ongoing operational support, monitoring and maintaining your cross-border connectivity to ensure stable production performance
Contact us to discuss your China deployment architecture.